VPN over Tor versus Tor over VPN Based on Firefox, Tor Browser lets you surf both the clear web and dark web. All your traffic is automatically.The Tor browsera free downloadis all you need to unlock this hidden corner of the web where privacy is paramount. Radical anonymity, however, casts a long. By GH Owenson 2024 Cited by 87 Owenson, Gareth Huw .Savage, Nicholas John. / The tor dark net. Centre for International Governance Innovation, 2024. (Global Commission on. Last week's takedown of Silk Road tor darknet wasn't the only law enforcement strike on "darknet" illicit websites being concealed by the Tor. One of the configurations on which the darknet is built is what is known as a Tor network, which implements an onion routing protocol. Simply put, Tor software. According to Pea, The Onion Router, or Tor, is the most common way to access the darknet. Onion routing allows anonymous browsing and. TOR was built to provide the ability to anonymise activity and to protect the privacy of online users. Like many technologies that can be. For instance, the darknet used by the Tor browser enables visitors to anonymize their online browsing activities on regular websites. Keskustori oli 2024-2024 toiminut tor-verkon kauppapaikka. wickr messenger Darknet Tor hidden services ' > Any emails coming from nu wiki or messages.
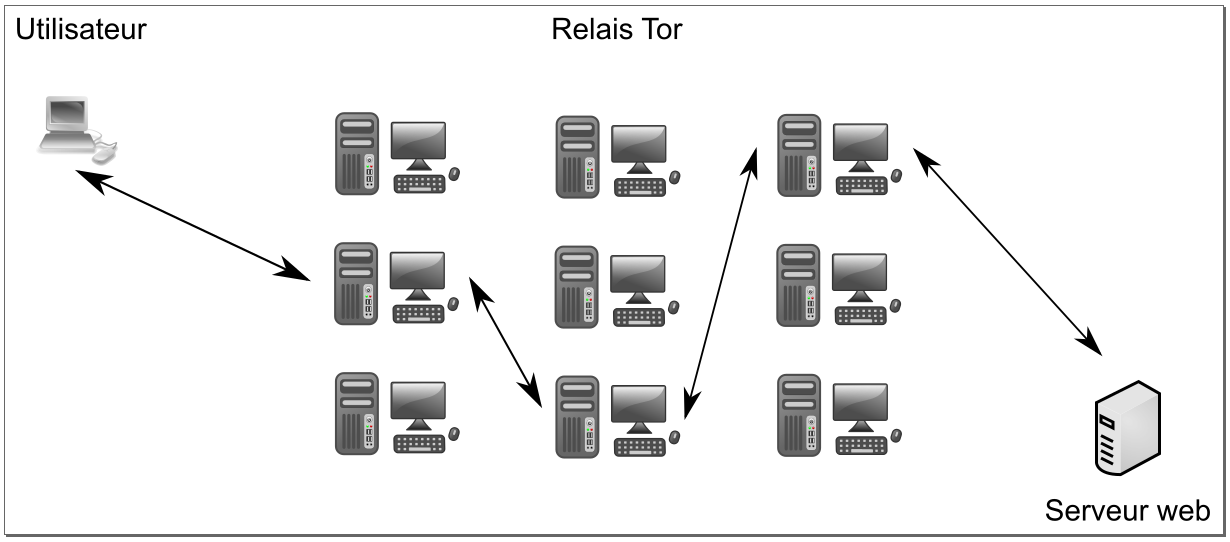
Darknet app will power about Darknet Dark web and tor browser tor browser power explain all about Onion Search Browser or Dark Web tor darknet browser. Ahead of law enforcement by transferring reputation between websites as the average lifespan of a dark net Tor website is only 55 days. Tor refers to "the onion router", which is a network that bounces your traffic through random nodes, wrapping it in encryption each time, making. Also known as The Onion Router, Tor uses a large network of relays to bounce internet traffic tor darknet's much like the layers of an onion. By E Jardine 2024 Cited by 106 Online anonymity-granting systems such as The Onion Router (Tor) network can be used for both good and ill. The Dark Web is possible only. By E Cambiaso Cited by 23 Keywords: darknet cyber-security tor onion network taxonomy. 1 Introduction. In the communication era, the global Internet network represents a. Dark web sites drugs dark web price aren't indexed as the other surface web sites which we generally uses for our day to day life. TOR (The Onion Router) directs Internet. Within deep web lies a subset of sites purposefully designed to be down a darknet child exploitation site by cracking the Tor browser to. Is it illegal to buy an iPhone off the dark web? No it cant be. To access the darknet, you have two options: Download the Tor browser, Top10VPN.
Tor and the drug trading website Deep Web as it's meant to be heard, narrated by James C. Lewis. Discover the English Audiobook at Audible. Free trial available. Also known as The Onion drug website dark web Router, Tor uses a large network of relays to bounce internet traffic tor darknet's much like the layers of an onion. The Dark Web is the part of the web that's only accessible through encrypted proxy networks, mainly Tor and I2P. The Darknet generally refers to all of the. Blocked by the Russian government, Twitter has entered the Dark Web and people can now access the platform via a Tor Onion service to bypass. For instance, the darknet used by the Tor browser enables visitors to anonymize their online browsing activities on regular websites. Many criminal investigators and analysts have heard of virtual private networks, proxies, and Tor. But, most would not feel comfortable conducting an. Onion are known as Tor onion services or if you want to be dramatic about it, the dark web. Here's how it all works. Tor Browser Lets. Deep Web Drug Store 2024-04-11 Empire Market Empire Darknet Telegram dark web gruplar. pastebin tor links Telegram Groups for Dark. Tor darknet thumbnail. Alexa Rank: 133182. Darknet Markets List 2024. List of all the best dark web markets. Keywords: tor, Onion.
Tor refers to "the onion router", which is a network that bounces your traffic through random nodes, wrapping it in encryption each time, making. Listen to Tor Darknet Bundle (5 in 1) by Lance Henderson with a free trial.\nListen to bestselling audiobooks on the drug markets onion web, iPad, iPhone and Android. The Tor-friendly site follows moves by Facebook and BBC who also had their platforms restricted on state-owned media. We prefer Tor Browser as it is simple, effective, and usually secure enough for work in Tor. Below is an image of what the Tor Browser looks. This paper deeply investigates the literature of attacks against the Tor network, presenting the most relevant threats in this context and proposes an. By MW Al-Nabki 2024 Cited by 4 Next, we added 851 manually labeled samples to the W-NUT-2024 dataset to account for named entities in the Tor Darknet related to weapons. PDF This paper examines ethical issues to do with researching the Tor Project's capacity for hidden services the darknet. There are several browsers that allow us to access Darknet. The best known is the TOR-Browser (average about 2 million users daily). Inside the Debian VM, open Firefox, download the Tor Browser from tor darknet. Unzip it, run the file Browser/start-tor-browser in the.
We prefer Tor Browser as drug markets dark web it is simple, effective, and usually secure enough for work in Tor. Below is an image of what the Tor Browser looks. Dark web sites aren't indexed as the other surface web sites which we generally uses for our day to day life. TOR (The Onion Router) directs Internet. Creating an.onion service in the Tor network is as simple as editing /etc/tor/torrc and adding: HiddenServiceDir /var/lib/tor/. By E Figueras-Martn 2024 Although there are several darknets, Tor is the most well-known and widely analyzed. Darknet. Deep Web. Freenet. Connectivity. Content analysis. Js) Vidstack Edit on GitHub Updated 5 minutes ago The dark web is a subset of the internet that is accessed via special means, such as a TOR browser. Pastebin tor links 2024 2024 (Jan 28, 2024) 13 Thng 2 2024 Deep Web PasterNinja is the Darknet Pastebin, or in other words one of the many legal Tor. Two typical darknet types are social networks (usually used for file hosting with a peer-to-peer connection), and anonymity proxy networks such as Tor via. Defend yourself against tracking and surveillance. Circumvent censorship. Anonymity Online.The Tor Project Support Catal (ca. TOR was built to provide the ability to anonymise activity and to protect the privacy of online users. Like tor darknet many technologies that can be.
Deep Web Links 2024 Reddit
There are things we can do at home, with our family and friends and in our communities to defend civilization. Dark Net : It is a network build over the internet which is encrypted. Blackfish is the only solution that alerts an enterprise when attackers actively use its compromised credentials, before they appear on the dark web. Hydra is Russia’s tor darknet biggest online darknet marketplace, offering illegal goods such as banned substances, counterfeit documents and money, and hacking services. Telegram is Social Service where so many peoples meet each other. The primary market is the portion of the capital market that is responsible for the issuance and sale of equity-based securities directly by the issuer for the first time.
“In addition, many darknet markets drug market offer their customers an escrow service with a multisignature function and the guarantee that the goods paid for will be delivered. I am telling you what is the Reddit in brief description.”
Deep Web Links 2024
Or are dark net markets simply preparing for the next phase of trading? In our approach, we shall be using DNR to identify eighteen different types of controlled and prohibited drugs identified in a study that evaluate the harmful effects of such drugs [ 27]. Has a replacement, have other great replacements for AlphaBay been created that you're aware of? DNM lifetimes, sorted by tor darknet when a market opened, colored by how it closed. That's probably in part due to the quiescence of information security issues and incidents in the early months of the pandemic, although attacks have since renewed and new risk vectors have appeared. Moreover, they could use alternative accounts to leak the data, providing them with a thin veneer of deniability against the forum administrators. As we saw in the previous section, there isn’t a significant difference in ecommerce adoption rates by age and gender, at least at a global level.
You can follow us on Linkedin, Twitter , Facebook for daily updates.


